A beginner's guide to analyzing the network traffic of apps and websites

You've no doubt heard this old proverb. Give someone a fish and you'll feed them for a day. Teach them how to fish and you'll feed them for a lifetime. The idea goes that someone in your life may teach you something you can use again and again, and that becomes a source of continuous reward.
This is the back-story of how I was taught to fish earlier in my cybersecurity journalism career.
Back in 2017, I was in contact with security researcher Will Strafach, who discovered that AccuWeather had embedded a piece of third-party code in its iPhone app that was collecting the device's location data, even if the iPhone's location setting was switched off.
This was an obscure finding, but a huge deal. It exposed that Apple devices weren't as private as users thought at the time, thanks to this loophole. It was also one of my first glimpses into the hidden world of third-party code and trackers embedded in apps and websites, and the voluminous amounts of data they collect while we use them.
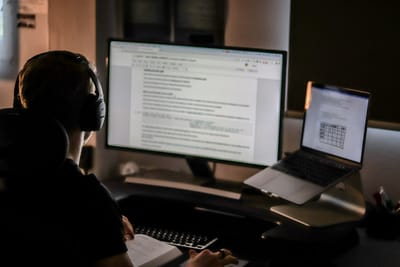
In explaining how the code worked, Strafach introduced me to Burp Suite, which is network analysis software that allows you to look at all of the network traffic flowing in and out of apps, websites, and devices by effectively wiretapping (or performing an adversary-in-the-middle attack) your own network connection.
This is helpful because what you see on your device's display isn't everything that happens when using an app or scrolling through a website. A lot is happening in the background, including the constant sending and receiving of data over the internet about your user interactions. Network analysis tools allow you to see exactly how an app or website loads, where it gets its content from, and where your data is sent.
Learning all of this was eye-opening. It was incredible to see this network traffic flow across my screen in a relatively easy-to-parse way as I used the app on my phone in real-time. It was magical.
But once you look behind the curtain and see what's actually happening, it can be both revealing and unsettling, knowing that there is this constant undercurrent of data that flows from your devices into the databases of big corporations.
I got hooked on Burp, learning to tinker with it more and more. In recent years, some of the big web browser makers have matched some of Burp's basic network analysis functionality, making these tools far more ubiquitous and available for anyone to use.
But, for me, learning to use Burp has been one of the most helpful things in my journalism career. It has helped me to:
- identify and expose countless spyware operations,
- find a major bug in a COVID-19 vaccination app used by several U.S. states,
- discover, report, and got fixed a data spill involving LabCorp patient data,
- earned a CVE for my reporting on a spyware exposing victims' data,
- find that USPS was sharing the home addresses of logged-in users with advertising giants like Meta, LinkedIn, and Snap,
- and, during 2025 alone, uncover and report several security and privacy flaws in popular apps, including viral call recording app Neon, event planning startup Partiful, and dating app Raw.
Suffice to say, it's been highly useful, and quite honestly it's been fun to learn along the way.
Almost a decade later, I sat down with a colleague at TechCrunch to teach them how to use Burp Suite to test one of those bizarre AI companion toys for suspected malfeasance (we found none). But within a few minutes, they'd already uncovered something buried in the Grok AI site, showing that it was able to pull out its hardcoded prompts that guide its responses.
It was really amazing to see them light up in equal parts excitement and horror using Burp Suite for the first time. I'm glad I was able to pass along some of these skills, and — just as Strafach had with me — teach them to fish.
Frankly, I think this is something that anyone can learn if you're interested, and the on-ramp to understanding is relatively easy. You can quickly learn how apps and websites really work by seeing the data flow in and out. You see how they function, what data they're sharing, and how frequently they're sharing your data, and with whom. And, in an age of vibe-coded apps that are slopped together by AI with minimal (or no) thought to security, Burp lets you perform basic app and website testing before you trust them with your own data.
It can be an enlightening, if not terrifying window into where your private data goes and who can ultimately access it.
Not just that, using Burp is a great way to learn how things work on the internet, and can be a foot in the door for further security research. I'm a firm believer that tech (and cybersecurity) journalists should try to learn technical skills throughout their careers. It's not an imperative, but building something — or breaking things — will help. Burp Suite, especially, is something anyone can learn to use, as it's free to download and tinker with its basic features.
In this incredibly deep-dive article (it's worth it!), I'll explain how to get started with Burp and similar browser-based tools. We'll talk about how APIs work, how to understand network requests, and I'll show you how to work with Burp Suite's most common tools. Plus, I'll walk you through a couple of examples of how I found some security flaws and exposures that I wrote up for TechCrunch.
Please consider a subscription to access this article! It helps to support long-reads like this, and gives you the tools you can use and how to use them.