this week in security — april 12 2026 edition
THIS WEEK, TL;DR
Russia's GRU hacked routers to hijack traffic and steal passwords
U.K. NCSC: If there's one thing you probably don't need in life is a Russian hacker in your router. But an operation uncovered this week found thousands of home and small business routers under the control of the Russian spy agency, GRU, which runs the notorious hacking unit known as Fancy Bear (or APT 28). By mass-hacking into TP-Link and MikroTik routers using known vulnerabilities, the hackers diverted victims' internet traffic to servers under their control using DNS redirection, then stole passwords and OAuth tokens of a more narrowed list of potential targets, with the aim of breaking into their online accounts. The FBI secured a court order allowing them to effectively hack into affected routers and remove the dodgy DNS records as the FBI has done with other botnets in the past.
More: Justice Department | Krebs on Security | The Register | HelpNetSecurity | Financial Times ($) | Cyberscoop
Iranian hackers targeting American critical infrastructure, per U.S. agencies
NBC News: Not wanting to be outdone by the Russians, Iran sparked a collective alarm from the FBI, NSA, CISA, and the Department of Energy after being caught targeting U.S. critical infrastructure, such as companies running energy and water systems. The warning said Iran-backed hackers are targeting these systems with the aim of causing "disruptive effects" to American critical infrastructure operators (though to what degree wasn't stated) in response to U.S. attacks on Iran. (Great job, U.S. government… two-thumbs up.) All to say, shields up, because we can likely expect more Iranian cyberattacks as the country appears to be firing back on all fronts, both digitally and militarily. Per Censys, there are at least 5,200 affected devices on the web in the sights of these Iranian hackers.
More: CISA | TechCrunch ($) | Censys
VeraCrypt, WireGuard devs couldn't send updates after Microsoft locks accounts
404 Media ($): Developers behind some of the most important software on the internet today found themselves locked out of parts of their Microsoft accounts, preventing them from releasing crucial updates to their Windows users. Microsoft had tried to verify them months ago so they could keep making drivers for Windows (which hackers also try to abuse), but the developers said that they never got an email. The maker of file encryption software VeraCrypt told me that if he couldn't update the software soon before its certificate authority expires, some of his users may face issues with booting up their PCs. (Disclosure: I wrote this!) VPN maker WireGuard also faced lockout issues, as did Windscribe and others. The good news is that Microsoft reversed course and got them back in and updates flowing, but Microsoft's messaging on all this — effectively blaming the user — was not less than great.
More: Hacker News | TechCrunch ($) | Bleeping Computer | @EdgeSecurity
Anthropic touts new model it won't release because it's too good at finding bugs
Wired ($): AI giant Anthropic has releas…announced a new model called Mythos that the company says is so good at finding security flaws, it can't broadly release or it'll basically rip the web apart. Instead, it's releasing it to a handful of big tech giants like Apple, AWS, Cisco, Google, the Linux Foundation, and others, so that they can effectively fix their own issues before the model invariably goes mainstream. While AI has been helpful in finding security flaws, many of these bugs still lack the ability to be exploited, something noted in this skeptic's take to Mythos. Gatekeeping this model also happens to also aid Anthropic's bottom line. Your skepticism here is welcome.
More: The Register | Business Insider | TechCrunch ($)
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for exclusive articles, analysis, and more.
~ ~
THE STUFF YOU MIGHT'VE MISSED
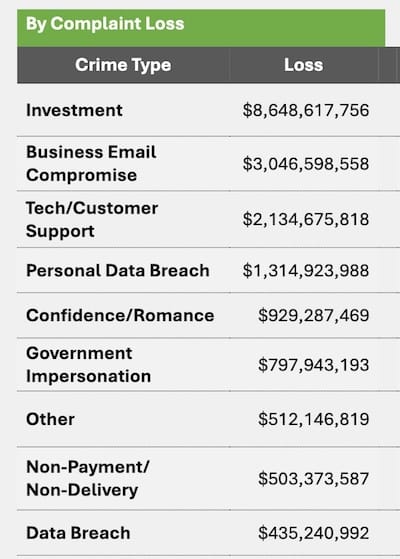
FBI says phishing and investment scams top 2025 cybercrime report
Cyberscoop: Financial losses associated with cybercrime went up by 26% in 2025, per the FBI's annual report detailing online threats. The report [PDF] lists phishing and spoofing taking the top slot in the number of complaints. Business email compromise (BEC) attacks, where hackers redirect payments to their own accounts, were second to the top of crime losses. Case in point: Zephyr Energy lost close to $1m after a hacker broke in and diverted a payment meant for a contractor, the company said this week.
How often do hackers default on promises to delete stolen data?
DataBreaches.net: The feds have long said not to pay a hacker's ransom, but new findings from DataBreaches.net explore why some organizations choose to pay hackers and why some victims don't, fearing that they can't trust a hacker's word.
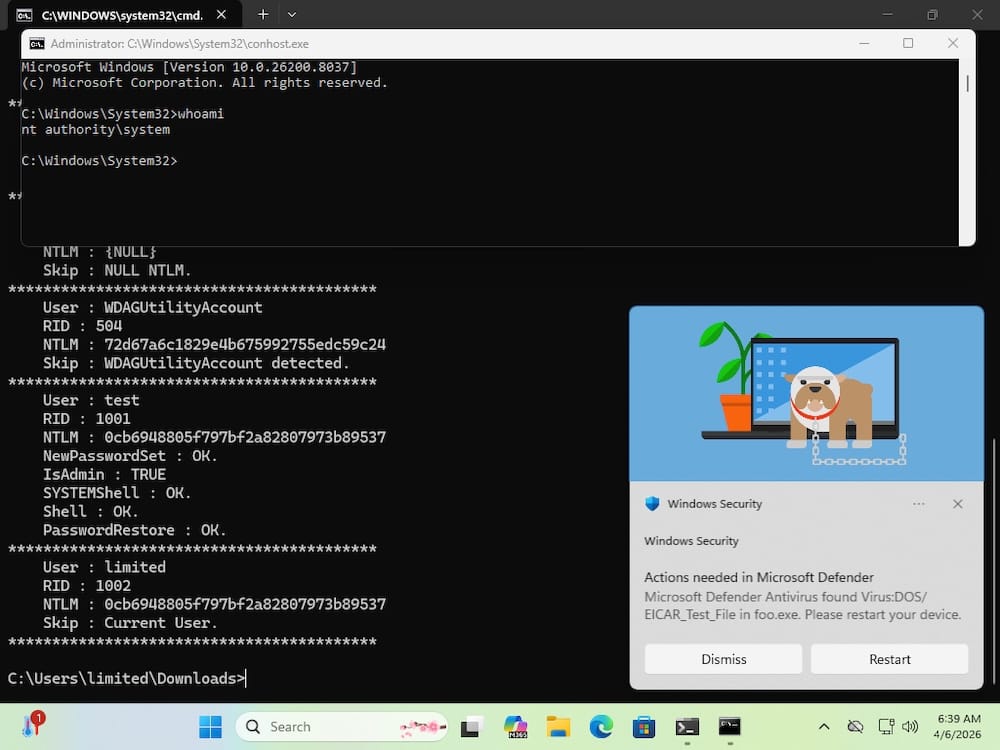
Disgruntled researcher leaks "BlueHammer” zero-day exploit for Windows
Bleeping Computer: A security researcher publicly dropped details of a Windows zero-day claiming Microsoft's allegedly lackluster handling of the bug report prompted them to release it. Don't panic just yet: While there's no immediate fix, the exploit (dubbed "BlueHammer") is quite buggy. When it does work, the exploit can allow access to the scrambled hashes of local account passwords, which may allow users to gain system-level privileges to the computer. Of course, @wdormann coaxed the bug into working. More via HelpNetSecurity.
'Mr. Raccoon' is hacking outsourcing giants to steal corporate data
SecurityWeek: A hacker that goes by "Mr. Raccoon" (I'm not making this up) has been caught stealing sensitive data from large outsourcing companies that do work for big tech and other corporate giants. The hacks rely on redirecting victims to fake Okta login pages and using fake Zendesk support lures. The hacker has already claimed to have stolen gobs of data from Adobe from an outsourcer in India. Google's Austin Larsen drops some guidance for defenders in a LinkedIn post.
~ ~
OTHER NEWSY NUGGETS
Convicted stalkerware maker avoids jail: Spyware scumbag Bryan Fleming, who founded and operated the now-defunct pcTattletale, has been sentenced to time served and a $5,000 fine after earlier pleading guilty to making, selling, and advertising spyware for illegal purposes. (Disclosure: I wrote this story.) Fleming avoided jail, but the prosecution leaves open the door to future criminal charges against other makers of spyware. (via TechCrunch ($), The Record, Cyberscoop)
Shiny hits Anodot users: ShinyHunters claim to have hacked Anodot, an integration software that lets users spot revenue anomalies in big data sets. Dozens of companies had data exfiltrated following the breach at Anodot, including Rockstar Games. Data giant Snowflake confirmed some of its customers are affected, and pulled the plug on the connector for the time being. Anodot's status page is a sea of red. (via Bleeping Computer, Kotaku)
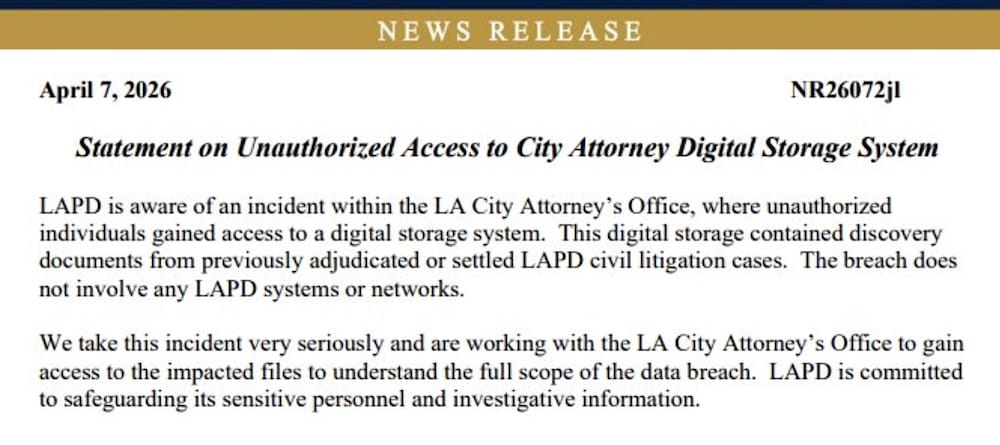
LAPD files swiped: The Los Angeles Police Department confirmed some of its data was stolen in a data breach at the city attorney’s office. The cache contains over 300,000 files, which may include sensitive and unredacted information about criminal cases. The leaked materials also include police records and personnel files, which are typically not released. Some city officials weren't aware of the incident until news reports emerged. (via LA Times ($), Spokesman-Review)
FBI nabbed Signal notification data: Feds retrieved a list of Signal messages by extracting the message contents from push notifications stored in their iPhone's logs, even after the app was deleted. You can (and should) change the app's notification settings. (via 404 Media ($), @raphae.li)
HackerOne had enough of AI slop: Bug bounty giant HackerOne has suspended its internet bug bounty program, which helps to find and patch bugs in open-source software. The company hinted that the reason was the rising number of AI slop reports. (via Dark Reading)
Spy powers certified, despite expiry: America's top surveillance powers, known as Section 702, are set to expire on April 20. But thanks to a weird quirk in how U.S. spy agencies are certified to conduct lawful surveillance on an annual basis by the secretive Washington DC-based court overseeing their powers — which happened this week — agencies like the NSA and FBI can continue spying for the next 12 months, even if FISA's legal authority expires… which, actually might! The White House wants a "clean" reauthorization, while Democrats aren't keen on handing Trump fresh spy powers on a plate. (via New York Times ($), Washington Post ($), Nextgov)
ChipSoft offlined: Electronic health records provider ChipSoft was hit by ransomware, nuking access to patient medical files across the Netherlands, where the software is widely used. (via Z-CERT, @patrickcmiller)
~ ~
THE HAPPY CORNER
Welcome back to the happy corner, your source of top-quality Good News™ on the weekend. There was me thinking I was having a good week, but it sounds like the internet's favorite industrial cyber sleuth @hacks4pancakes had an even better Friday.
In news that I can barely believe… a startup only went and made Doom run on brain cells. Yes, in this edition's What Can Doom Run On?, we have hundreds of thousands of actual neurons capable of playing the first-person shooter game, according to The Economist ($). The aim is to develop new kinds of low-power computers and potentially pave the way for neurological drugs. Now, getting the neurons to actually play Doom well, that's a whole other challenge. (Thanks to the anonymous tipster for sending in!)
And, since it's a quiet-ish one, here's a bonus chopstick thief cybercat.
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
This week's cybercat is Sage, who can be seen here basking in the beautiful sunlight as he contemplates the world. Sage's human tells me that he has been unwell of late, and so we're sending the collective love and support of this newsletter to Sage and his humans. All our very best to you, and thanks so much for sending in, Oscar!

🐈 Send in your cyber cats! 🐈⬛ Got a cat or a non-feline friend? Send me an email with their photo and name and they will be featured in a later newsletter!
~ ~
SUGGESTION BOX
And that's all there is for the news this week, thanks so much for powering through — what a week, huh!
As always, please get in touch if you want to share anything for the newsletter. You can reach out by email anytime. It's always lovely to hear from you, and I always appreciate the stream of tips, stories, and fun stuff for the happy corner.
If you haven't yet checked out my articles, please do! I'd love it if you considered becoming a paying subscriber if you're able to. And don't forget there's also some 7+ years of newsletters (and security history!) in the archives for your perusal.
Have a peaceful rest of your weekend, and enjoy the rest of your week. It looks like Fools Spring I, II, and III: Fool Me Thrice have been and gone here in the New York tri-state area so I'm hoping that this week of expected warmer weather will finally stick and the cold is behind us for the season.
All my very best,
@zackwhittaker