this week in security — april 19 2026 edition
THIS WEEK, TL;DR
U.S. lawmakers punt FISA surveillance law vote until April 30
Associated Press: Will they or won't they? Well, neither, as it happens. Congress, once again, is punting its all-important vote on whether it will extend the U.S. surveillance law known as Section 702 of FISA until the end of the month. Lawmakers remain split on whether to reapprove or reform the law, despite decades of abuses and scandals involving spying on Americans (who are meant to be exempt!). Among the key bipartisan reforms include ensuring the feds need a warrant before reading an American's data (even if it was collected by mistake) or buying data from commercial data brokers. But instead of buckling down and making a decision, lawmakers voted to extend the deadline until… April 30. So, let's do this all over again in a couple of weeks, yeah?
More: Axios ($) | Nextgov | Lawfare | TechCrunch ($) | Techdirt | Politico ($) | Cyberscoop | @wyden
Microsoft patches second-largest monthly round of security bugs
Krebs on Security: Microsoft has patched a monster 163 software vulnerabilities across its software lineup during its monthly roundup of security fix releases. Zero-day documenter Dustin Childs said that this was the second-largest round of updates in Microsoft's history. It's not clear exactly why the sudden bump. Only one bug has been exploited in the wild (at the time of patching), specifically a bug in SharePoint that allows attackers to view and change sensitive information. Separately: A bug dubbed BlueHammer, which Microsoft allegedly didn't patch and so a disgruntled researcher released proof-of-concept code, has now been fixed, but not before the public code was exploited by malicious hackers in an attack, per @HuntressLabs.
More: Cyberscoop | Zero Day Initiative | Qualys
Pro-Russian hackers tried to breach Swedish power plant, but failed
Reuters ($), SVT: Sweden's minister for civil defense accused hackers linked to Russian intelligence of trying to carry out a "destructive" cyberattack against a thermal power plant in the west of Sweden last year. The attack failed, but was enough for the Swedes to go public now that the immediate threat has passed. Not so much for the rest of Europe though, since this is the latest in a string of attacks blamed on Russia in recent years targeting critical infrastructure like water and energy systems, from things like power blackouts to the malicious opening of dam floodgates. Sweden sounded this alarm as it claims these hacks were "riskier and more reckless behavior" from the Kremlin.
More: SVT ($) | EnergyWatch | TechCrunch ($) | Euronews
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for exclusive articles, analysis, and more; or, submit a one-time tip to show your support!
~ ~
THE STUFF YOU MIGHT'VE MISSED
100+ cyber leaders publish report on preparing for AI cyberattacks
Cloud Security Alliance: Over a hundred of the smartest people in cybersecurity have come together to coauthor a report that outlines some of the most pressing risks from AI systems that are capable of finding new software bugs and, in some cases, exploiting them. This read is a detailed "how to" get started defending against what is expected to be an upcoming wave of future hacks. It's free to read [PDF], so there are no excuses! More in a summary by Ricki Burke, but I would recommend reading a blog by Bruce Schneier, a co-author of the report, who just cuts straight through the noise in a four-point list of bullets.
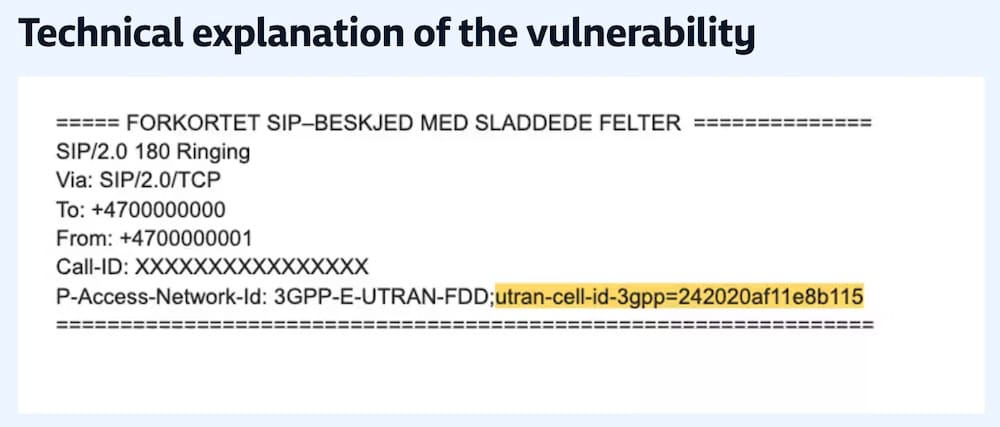
Norwegian telco was accidentally leaking customers' location data
NRK: For years, some customers at Norwegian phone company Telia have been publicly trackable because the company was leaking users' location data over the network's airwaves when customers make or receive a call. Some customers' location data was tracked to the nearest cellular base station, which can be down to a few meters. The news comes weeks after U.K. telco O2 had a similar bug leaking users' location data.
Someone bought 30 WordPress plug-ins and planted the back door and all of them
Anchor Hosting: A new nightmare scenario unlocked: Someone bought a company that provides WordPress plugins and planted a backdoor in the code, allowing the new owners to get access to potentially hundreds of thousands of customer websites. The plugins can't be downloaded anymore from WordPress' plugins site, but existing WordPress installations might still be at risk. (via @britt)
PowerSchool hacker discusses hack while in prison
ABC News: Matthew Lane, the then-teenager who hacked ed-tech giant PowerSchool and stole tens of millions of kids' private data, begins his prison term for the massive data beach. Lane spoke about how he got caught up in the cybercriminal world at a young age. The piece acknowledges the harms that Lane caused but also focuses on the need to rehabilitate and redirect young hackers into schemes and programs that better them and cybersecurity at large. Lane royally screwed up with his actions, but as a child at the time, it was adults that failed him.
A giant surveillance tower on the Mexico-Texas border is ready
Rest of World: A 20-floor tower dubbed the Torre Centinela (Sentinel Tower) in downtown Juárez on the Chihuahua-Texas border is now watching over a vast swath of land after years of construction. This surveillance hub has already sparked considerable alarm by privacy advocates on both sides of the border, given that there's a data sharing agreement between Texas authorities and Mexico. One concern is that this agreement "could be used to detain and deport migrants." The EFF has updated its guide on tech and surveillance at the U.S.-Mexico border.
Cargo hackers are helping criminals steal delivery trucks packed with goods
Proofpoint: A truck of vapes here, a lorry of lobster meat there. Now, it seems someone made off with twelve tons of KitKat chocolate bars. No, this isn't just a snacky hijacker (though that would definitely be my hacker handle), but what researchers say is a growing collaboration between hackers targeting cargo companies, and then feeding the information to criminal gangs who hijack delivery trucks. (For paying subscribers: I also wrote some words ($) about this!)
Madison Square Garden's boss has built a creepy surveillance empire
Wired ($): Wired has the inside story of how Knicks owner and CEO of Madison Square Garden, Jim Dolan, uses facial recognition and other surveillance to target his critics, including in one case a child(!) in Colorado. Dolan's surveillance system rivals that of an intelligence agency. Why? Because Dolan is a creep and a weirdo, end of. But the story itself is definitely worth your time, even if you'll hate what you read.
~ ~
OTHER NEWSY NUGGETS
Basic-Fit's basic security: European gym giant Basic Fit confirmed a data breach, affecting at least a million customers, and some 200,000 in the Netherlands alone. The affected information includes names, dates of birth, postal and email addresses, phone numbers, and bank account details. (via Basic-Fit [PDF], The Register)
Booking.com breached: Not to be outdone, Booking.com told an unknown number of customers that an unauthorized party accessed their personal information and travel details. No details on who or what, exactly, and the company wouldn't say, but that data wasn't accessed from Booking's systems directly. That could suggest that a hotel's check-in systems were compromised. (via 9News, BBC News ($))
Rockstar Games, Kraken extorted: Grand Theft Auto game maker Rockstar had a ton of its analytics data published online by the ShinyHunters hacking and extortion gang. The company's breach was linked to the earlier hack at Anadot, which Rockstar and other tech giants rely on. Meanwhile: Crypto exchange Kraken says it's also being extorted by a group that claims to have access to some client information. (via Bleeping Computer, Bloomberg ($), @c7five)
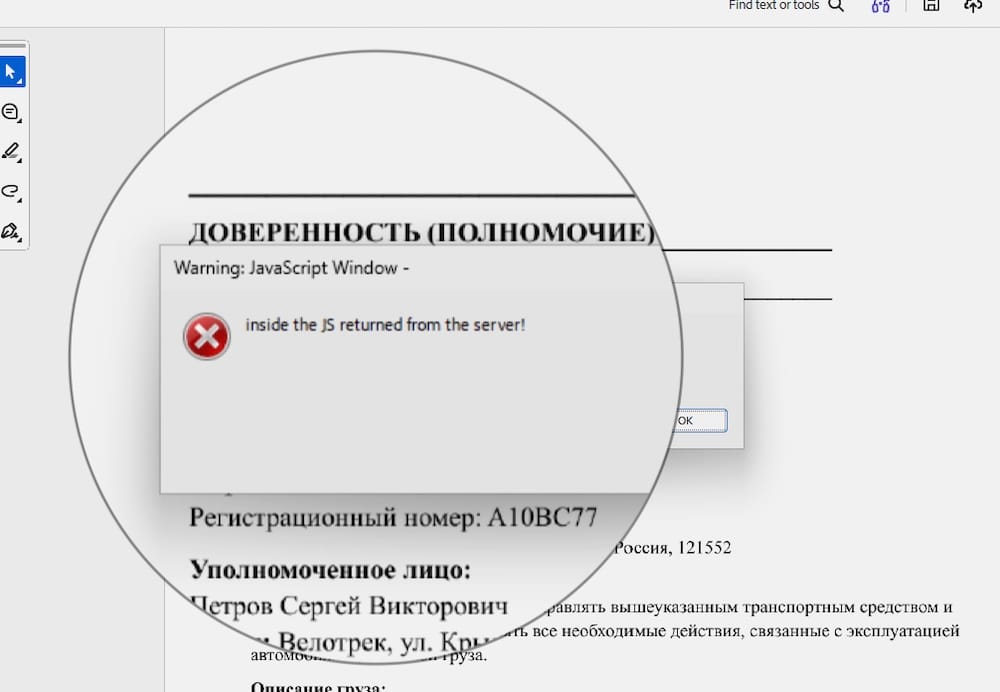
Adobe fixes months-old PDF attack: Adobe has fixed a zero-day in its PDF reader software that allows hackers to remotely plant malware on a victim's computer by simply opening a malicious PDF with its software. Haifei Li found the exploit and wrote up its findings. Per Li, an earlier copy of the malicious PDF was also found on VirusTotal as early as November 2025, suggesting this hacking campaign has been going on for months. (via Adobe, TechCrunch ($))
North Korean facilitators jailed: Two New Jersey residents, Kejia Wang and Zhenxing Wang, were jailed this week for their role in facilitating North Korean IT worker schemes in the United States, helping the regime earn millions to fund its nuclear weapons program. The two stole Americans' identities to help North Koreans gain employment to earn a wage. (via Justice Department, SecurityWeek)
~ ~
THE HAPPY CORNER
If that was the news, this is your peaceful space: Welcome back to the happy corner.
Firstly, I'm absolutely thrilled to be back so soon with a brand new What Can Doom Run On? From brain cells to earbuds…. Now we can play Doom over… cURL? I can certainly see this being a win for all the folks who love using the terminal, but otherwise I'm glad the developer answered a key question of mine.
Also, don't miss Doom on a toaster. I'm sorry but this is absolutely insane and I'm also so very here for it. I don't think we can do any better than this. Prove me wrong, internet?

A regular reminder that @jerry, who runs the Mastodon infosec.exchange — home to infosec and security pros around the world — is the best and we can all be incredibly thankful for this community. Per a post this week, there's also a lot more in the wider infosec family of sites to check out. If you can, you can donate to support!
Ever need to disable biometrics on your macOS computer for security? Easy done, as it turns out, and now there's an app for that, called Panic Button.
And lastly, enjoy this ~inspirational quote~.
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
This week's cyber cat pupper is Winnie. That's the look of a happy, chill, and comfortable cyber-pup who knows that all their accounts are two-factored to the max and secured to the hilt. No hackers are getting by Winnie today. A big thanks to Scott for sending in!

🐈 Keep sending in your cyber cats! 🐈⬛ Got a cat or a non-feline friend? Send me an email with their photo and name and they will be featured in a later newsletter!
~ ~
SUGGESTION BOX
That's all from this week. I won't keep you for another moment. But you know the drill: See something, say something, and it might just end up in next week's newsletter.
Wherever you are in the world, thank you so much for reading, and I hope you enjoy the rest of your week.
Have a good one,
@zackwhittaker