this week in security — march 1 2026 edition
THIS WEEK, TL;DR
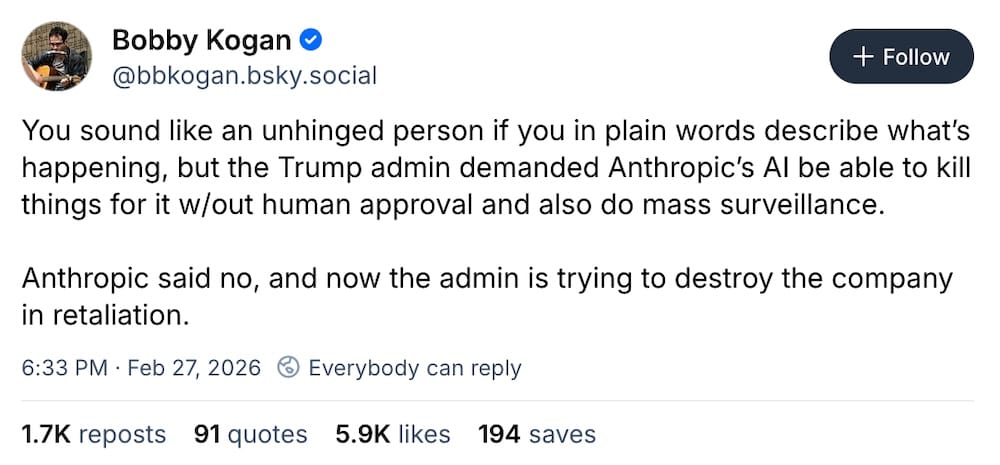
U.S. blocks Anthropic across government over its refusal to allow AI for mass surveillance and autonomous weapons
The Atlantic ($): We start with AI giant Anthropic, which was unceremoniously booted from the U.S. government after the company refused to allow the Trump government to use Anthropic's unthrottled Claude AI for mass surveillance or fully autonomous weapons (assuming the tech can do this to begin with). Trump retaliated, designating Anthropic a supply chain risk to national security, basically destroying the chances of any startup making it in the U.S. in the future: Give in, or we'll make it impossible for you to operate. OpenAI stepped up instead, allowing the use of its AI on classified networks, suggesting it'd be willing to give the government something that Anthropic wasn't. All the while, the U.S. still used Anthropic's Claude in Saturday's air strikes on Iran! Maybe there's a lesson here in not developing tech that can be used to spy on or kill people? Just a thought.
More: Associated Press | The New York Times ($) | TechCrunch ($) | Wired ($) | Techdirt | EFF | Tech Policy Press | @sarahjeong | @kevincollier
The inside story of how a hacking unit boss leaked hacking tools to Russia
TechCrunch ($): Peter Williams, the former boss of L3Harris' hacking tools maker Trenchant, will spend at least seven years behind bars after pleading guilty to stealing and selling eight exploits from his employer to a Russian broker, now sanctioned by the U.S. Treasury. A federal court sentenced Williams this week. @lorenzofb, who investigated the story and first broke the news of Williams' conduct, dug into how he reported the story and how it came to be — as well as his outstanding questions. Chiefly, given that the exploits sold on were capable of hacking "millions" of devices globally, did Trenchant ever disclose the bugs to the software vendors to fix, or are millions of devices still sitting ducks?
More: TechCrunch ($) | ABC.net.au | @patrickhowelloneill | Cyberscoop | @kimzetter
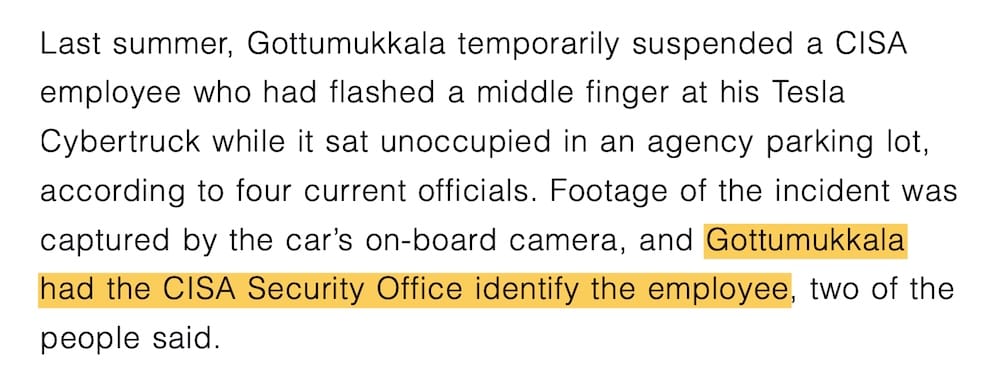
Acting CISA director replaced after a bumbling year on the job
Nextgov: Madhu Gottumukkala, the acting director of U.S. cybersecurity agency CISA, has failed upwards to a new position at Homeland Security, with Nick Andersen replacing him as the new acting head of CISA. ABC News broke that Gottumukkala was leaving after a year of bumbling the job. Aside from Trump cuts, layoffs, and staff reassignments, including to other agencies to support the broad immigration crackdown, Gottumukkala had his own tumultuous run. Per Politico ($), he failed a polygraph and uploaded sensitive government files to ChatGPT. All the while, Sean Plankey, the government's pick to lead CISA on a permanent basis, still hasn't had a Senate nomination hearing — more than a year after being chosen and having to be re-nominated again this year — because CISA won't release an unclassified report into the sorry state of cybersecurity at U.S. phone giants. Meanwhile: Trump's pick to head the NSA spy agency, Joshua Rudd, is also on hold, with one senator saying he's not qualified for the job.
More: Healthcare Infosecurity | Cyberscoop | The Record
Marquis sues SonicWall over firewall breach that led to ransomware
TechCrunch ($): Grab your popcorn, this could be one to watch. Fintech company Marquis is suing its firewall maker SonicWall, claiming its data breach last year allowed hackers to steal a firewall backup file from its cloud servers that allows the hackers to subsequently break into Marquis, steal gobs of data, and deploy ransomware. SonicWall previously admitted that every customer who uploaded their firewall backup files (which allegedly contain sensitive codes that can be used to bypass their security) to its cloud may be affected, and not 5% as it first claimed. If Marquis wins, it could open SonicWall to a fire…storm of liability. (Disclosure: I wrote this story!)
More: DocumentCloud | Bleeping Computer | BankInfoSecurity | CU Today | SC Media
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for exclusive articles, analysis, and more, including:
Apple's Lockdown Mode: Once an 'extreme' security protection, now a necessity for Americans
ClickFix attacks are increasingly devious, dangerous, and can hack you in an instant
~ ~
THE STUFF YOU MIGHT'VE MISSED
Ad tech giant Optimizely hacked and data stolen
SecurityWeek, DutchNews.nl: The ShinyHunters gang are on another hacking tear, targeting a bunch of companies with voice-based social engineering attacks (think tricking employees into handing over access to internal systems). Ad tech giant Optimizely said its Zendesk and Salesforce databases were raided, and other systems compromised, spilling "basic business contact information," in a breach thought to be linked to ShinyHunters. Vehicle marketplace CarGurus was breached, allowing the theft of names, phone numbers, and home addresses of around 12 million users. But Dutch telco Odido fared worse, with over 6 million people having their data published over several days this week after the company refused to pay their ransom. DataBreaches.net has more analysis.
Major New Zealand health app breached and data changed
1News: A very strange situation where a popular Kiwi medical data records company was breached and records apparently defaced and modified, while others were marked as deceased. MediMap is used for communicating medication doses, so… uh, not great. More via Stuff.co.nz.
U.S. and allies sound alarm on latest Cisco zero-day, dating back to 2023
Help Net Security: Hackers (origin or affiliations unknown) have been exploiting a zero-day bug in Cisco's SD-WAN products since at least 2023. The newly discovered bug, tracked as CVE-2026-20127, is rated top-severity as it can be used to bypass authentication on the device and access a company's network. The Five Eyes sounded the alarm, urging customers to patch. CISA has a few words for network defenders.
Log4j says AI slop reports are hurting its bug bounty
Apache, GitHub: Vulnerability reports written and submitted by AI are hurting highly popular open-source projects like Log4j. The developers said they've been inundated with slop reports reporting vulnerabilities that aren't really actually that big of a deal. AI might be somewhat helpful in finding bugs, but if we can't categorize or triage them for severity, we're just going to deluge developers with noise. Remember, it was Log4j that back in 2021 sparked a global response to fix a zero-day under attack, prompting the creation of the Cyber Safety Review Board. Have we learned nothing?
New Airsnitch attack breaks Wi-Fi encryption at home and offices
Ars Technica: Your guest Wi-Fi network might not be as isolated as you think. A new attack dubbed AirSnitch can bypass client isolation, allowing guest Wi-Fi users to hop to the regular Wi-Fi network and potentially access to other devices on the network. The attack can be exploited across a range of routers. @vanhoefm has some added context.
~ ~
OTHER NEWSY NUGGETS
Lawmakers call for snooping transparency: A bipartisan Senate bill aims to require the disclosure of thousands of U.S. surveillance orders each year, even when targets aren't charged with a crime. The bill, if it becomes law, will notify people when their emails, locations, or browsing history have been requested. (via Ron Wyden, ProPublica)
U.S. to fight data sovereignty: If you haven't got a plan to take your data out of U.S. hands, now might be a good time, as the U.S. government is fighting international efforts by governments to regulate how U.S. tech giants handle personal data (such as Europe through trade deals and its GDPR privacy rules). Some countries are increasingly wary of how the U.S. is handling itself, and therefore concerned about the data that they store with U.S. tech giants. Also, alarm bells rung as Trump may enlist banks into collecting people's citizenship data, which hasn't been done before. (via Reuters ($), Wall Street Journal ($))
Amazon changes dox addresses: If you have an Amazon wish-list (teachers, too, because America), be warned: A planned change means if someone buys something from your wish-list, it could expose your delivery address. (via 404 Media ($), @josephcox)
Kansas revokes driver's licenses of trans folks: Horrific news out of Kansas, where lawmakers passed a surprise bill invalidating the driver's licenses of trans people (with no grace period) whose gender marker doesn't match their birth certificate. This is really bad for trans people and a huge erosion of civil rights for everyone. Trans rights are human rights. “I worry that the [Trump] administration could start going after us with that information like they have for immigrants,” per someone who is affected by this. (via Erin In The Morning, The Handbasket)
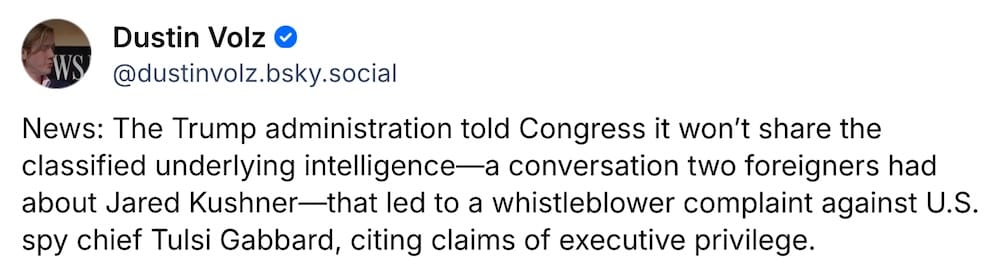
U.S. blocks lawmakers from whistleblower complaint: About that whistleblower complaint… It looks like Congress won't see the unredacted intelligence that seemed to suggest Trump's son-in-law Jared Kushner was brought up during a phone call by foreign nationals relating to Iran. The administration says the "claims about Kushner were demonstrably false," but… uhhh, how do we know if even our lawmakers don't know? Absolutely nothing suspicious to see here! (via Wall Street Journal ($), @dustinvolz)
A Wynn for hackers: Hotelier giant Wynn says hackers stole employee data from its servers, but claims the hackers deleted the data, strongly suggesting the company paid the hacker's ransom. The feds say not to do this because the hackers just keep coming back for more. (via The Register, Las Vegas Review-Journal)
…and a huge loss for France: Hackers nabbed medical records on some 15 million people across France. The data, as you might expect, contains highly sensitive health information, including diagnoses. The hack targeted the software maker Cegedim Sante in late 2025. (via France24, BFM, DataBreaches.net)
~ ~
THE HAPPY CORNER
Alright, let's try to leave some of the doom and gloom behind (this year so far has been a mood) and welcome to the calm, gentle place we call the happy corner.
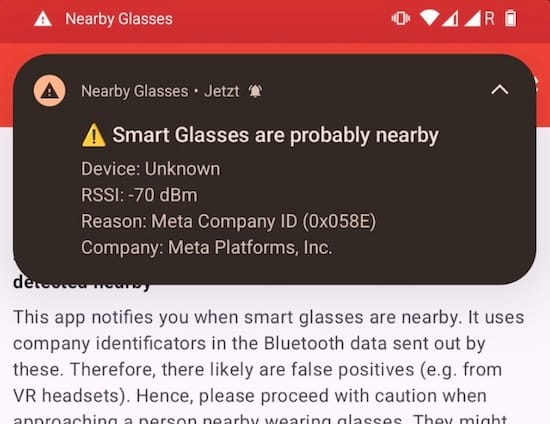
Beware, glassholes! This new app scans for nearby Bluetooth signals emitting from smart glasses (with cameras baked-in) and alerts you if it identifies someone wearing "luxury surveillance." More via 404 Media ($) and @yjeanrenaud on GitHub.
Proof that sometimes bad things can happen to bad people: Four executives, including the founder, behind the Predator spyware maker Intellexa, have been sentenced to jail following a Greek court case investigating the abuse of its spyware to snoop on the phones of dozens of journalists and politicians. If you recall, "Greek Watergate" gripped the country for years, though no government officials have been charged with deploying the spyware. Still, this is the first known time individuals involved with making spyware have been sentenced to jail following the misuse of its tech. (More via @sophieintveld.)
And finally. This new privacy screen feature built-in to the software in Samsung phones to stop shoulder-surfers peeking at your private messages is pretty cool. Can everyone else have this, too? (via Pixels & Pizza, 9to5Google)
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
This week's cyber cat is Whisper, who is taking a moment to relax after a very difficult day after red-teaming. She looks cute, but she can swipe your two-factor codes from you in an instant. Time to log-in and buy some treeeeeaaats! Thanks so much to Radek for sending in!

🐈 Please send in your cyber cats! 🐈⬛ Got a cat or a non-feline friend? Send me an email with their photo and name and they will be featured in a later newsletter!
~ ~
SUGGESTION BOX
Let's call time on whatever that hellish week was! Thanks for making it through, and reading this week's edition.
Catch me next week with your usual roundup from the past seven days. As always, I really appreciate hearing from you, so get in touch with anything you want to share for the newsletter. And please do send in your cyber-cats (or their friends!).
Have a peaceful week,
@zackwhittaker