this week in security — march 29 2026 edition
THIS WEEK, TL;DR
Iran-linked Handala hackers breach Kash Patel's personal email
Reuters ($): Not a great look for the head of one of the U.S.' top intelligence agencies: Iran-linked Handala hackers took credit for raiding the personal email account of FBI director Kash Patel, stealing and publishing caches of files, emails, and more in what looks like a classic hack-and-leak operation, which Iran is known for. Much of the data is old, dating between 2012 and ~2019-ish, but as noted by @WilliamTurton, at least one email is from 2022, suggesting more may leak. At TechCrunch ($) (disclosure alert!), we verified the authenticity of the emails by checking the cryptographic signatures in the message headers. The FBI confirmed it was aware of Patel's email breach. It's not clear yet how Patel's email account was breached, but @vxunderground suggests it's possible he reused his Gmail password on another account that was stolen in a data breach.
More: TechCrunch ($) | The New York Times ($) | Straight Arrow News | NBC News | @raphae.li posts
iOS hacking tool DarkSword leaks online, putting older devices at risk of data thefts
TechCrunch ($): Last week's story about iOS exploits, dubbed DarkSword, which can hack into people's iPhones and iPads simply by someone visiting a malicious site, is now so much worse. The exploits leaked online and were published on GitHub, allowing anyone to set up their own malicious websites and start hacking people who are running older, out-of-date iOS software — not great! Researchers say malicious hackers are already using these tools in active hacking campaigns to steal data from people's devices, so update today. iVerify has a proof-of-concept video showing how DarkSword works. Apple says users running the latest iOS 15 through iOS 26 are protected, and that Lockdown Mode, which continues to repel spyware attacks, also helps repel these specific attacks. @lorenzofb has a Q&A that explains this shituation (not a typo) well.
More: TechCrunch ($) | Cyberscoop | @zeroxjf
U.S. FCC bans new, foreign-made routers, citing 'cybersecurity'
The Verge ($): Just months after it was rumored that the U.S. would ban TP-Link, one of the biggest router makers, the FCC has ordered the import ban on all new foreign-made routers, citing cybersecurity risks, effectively carving out a perfect market for U.S. router makers instead given that the majority of routers are manufactured overseas. While this won't affect older or current models in homes or on shelves today, it will affect new imports. Routers are often buggy, but newer models are getting better at security. The FCC blamed Chinese hackers Salt, Volt, and Flax Typhoon for hacking into routers around the world, but neglected to note that these hackers often targeted vulnerabilities in U.S.-made routers, like routers made by Cisco! Shy any technical reason for the ban (and there doesn't seem to be one), this certainly looks like a legally questionable shakedown that gives Trump sole authority to grant new router imports from overseas.
Archive: this week in security | More: FCC | Techdirt | PCMag | BBC News ($)
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for exclusive articles, analysis, and more.
~ ~
THE STUFF YOU MIGHT'VE MISSED
Israel hacked Iran's vast camera network to spy on its top leaders
Associated Press: Excellent reporting here by @dakekang and @sammednick. Soon after the assassination of Iran's supreme leader, the Financial Times ($) initially reported that Israel had hacked traffic cameras around Tehran to identify where senior government leaders would be. The AP's latest work digs into the story further and shows how this vast network of cameras was used against Iran's own government, in some cases thanks to incredibly weak passwords.
A cybercriminal crew is stealing a ton of data by hacking open-source projects
OpenSourceMalware: A messy cascading set of hacks blew up this week after a hacking crew called TeamPCP compromised several open source projects, starting with the Trivy security scanner by Aqua Security. This allowed the hackers to push credential stealing code affecting other open-source projects, like Aqua's Docker images, Checkmarx's KICS project, and now LiteLLM. (The full campaign is logged as CVE-2026-33634. Ars Technica has more.
U.S. grid growing more vulnerable to cyberattacks, per official
Semafor: In an unusually candid but frustratingly short exchange, top U.S. energy official Alexander Fitzsimmons said while the U.S. has so far avoided a large-scale breach of the energy grid, he's concerned that hackers could have hacked into the IT networks of critical infrastructure to strike at "a time and place of their choosing.” That sounds a lot like China's Volt Typhoon, which is known specifically for targeting critical infrastructure and military bases with malware, likely to cause disruption ahead of its anticipated future invasion of Taiwan.
Police are using Google cookies to unmask anonymous users
Forbes ($): Police asked Google for information relating to an anonymous Gmail account that was allegedly used to send a hoax bomb threat. Police then asked if anyone else had accessed this account. A cookie, which is a tiny piece of code that keeps you logged into apps and websites without having to constantly reenter your password, showed that the account was logged into an iPhone alongside another Gmail account, which was registered with the person's real identity. Opsec fail.
How selling snoop tech to a repressive regime almost broke Sandvine
Bloomberg ($): @rjgallagher, who's been covering Sandvine for years, has a deep-dive look-back story at how the maker of web security tools slid into becoming a major surveillance provider for authoritarian regimes. This goes to show that if you build something that could be used for surveillance, it will eventually be used for surveillance.
Hackers abuse Railway to send phishing emails that hijack Microsoft accounts
Cyberscoop: Huntress security researchers say a new hacking campaign that relies on sending emails via AI cloud hosting service Railway has successfully stolen credentials and granted access to hundreds of Microsoft cloud accounts. The campaign relies on a weakness in Microsoft's authentication flow for smart devices, printers, and terminals, without needing to steal passwords. Hundreds of companies have fallen for this campaign so far.
~ ~
OTHER NEWSY NUGGETS
VPN for me, NSA snoops for free: Using a commercial VPN to bounce your internet traffic outside the United States and to the broad world might actually make it easier for U.S. intelligence to snoop on that data. The NSA already buys internet traffic, but quirks of how U.S. law ostensibly "limits" snooping on Americans (heavy quotes, because it doesn't really), the NSA might see and collect overseas internet data and not realize it belongs to an American. (via Wired ($))
Your private Zoom call is now a nightmare podcast: If you've ever posted a Zoom link to the internet, there's a good chance it might've been scraped, accessed, watched, and turned into an AI-generated podcast by a startup called WebinarTV. All the more reason to practice safe meeting security and keep those links private! (via 404 Media ($))
Crunchyroll probes data breach: Anime site Crunchyroll confirmed a data breach after hackers claimed to have stolen 6.8 gigabytes of user data from the platform. Per Bleeping Computer, the hacker reportedly broke in by accessing an Okta account of a Crunchyroll support employee working for outsourcing giant Telus Digital (but note that it's apparently unrelated and separate to that ongoing Telus incident). (via TechCrunch ($))
New DHS secretary, who dis? Oklahoma senator and Trump fan, Markwayne Mullins, is the new head of U.S. Homeland Security and its enormous surveillance and monitoring apparatus. Mullins, whose confirmation hearing included details of his threats of violence against children, now heads agencies like CISA, ICE, and also TSA, which is currently without any money to pay airport screening staff.
Dutch gehackt! The Dutch Finance Ministry says it was hacked, causing an outage that's making it difficult for government workers to, well, work. The breach happened on March 19 and affects the ministry's policy unit. (via Rijksoverheid, Bloomberg ($), NL Times)
Edtech giant Kaplan breach deepens: Some 1.4 million people had data stolen in a data breach affecting education tech provider Kaplan, after reporting hackers were in its systems between October 30 to November 18, 2025. The hackers had access to names, Social Security numbers, and driver’s license numbers. (via The Record, @jgreig)
Bank glitch exposed half-a-million people's transactions: Close to 450,000 customers of Lloyds Bank in the U.K, had their financial transactions and sensitive personal information, like National Insurance numbers, exposed to other customers in an app glitch. In a letter [PDF] from its banking boss, the IT glitch meant a "customer had to access their own list of transactions within small fractions of a second of another person doing the same." I asked about this on ~the socials~ and the consensus suggests the issue may be related to caching. (via The Register, Reuters ($))
~ ~
THE HAPPY CORNER
Welcome back to the happy corner, where it's nothing but good news and fun stuff from here on out.
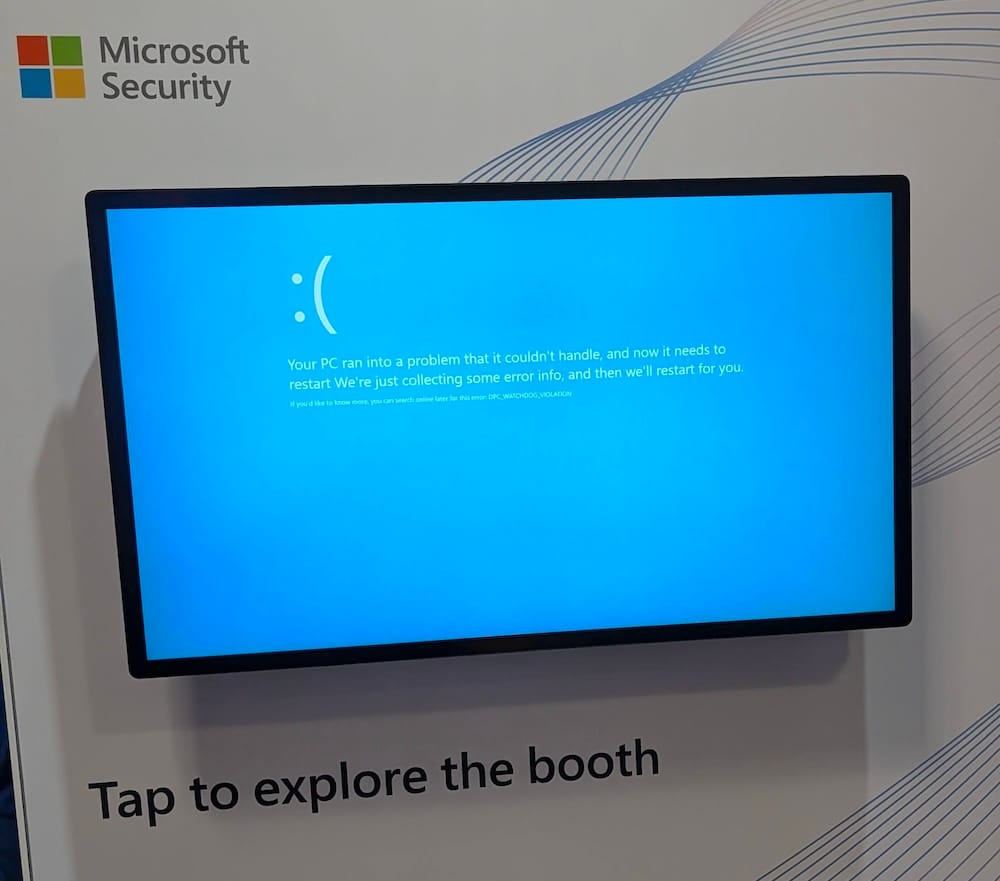
If you went, how was your RSA? Hope you had fun, saw old friends and met some new people. Maybe you checked out some booths? Microsoft's seemed to be going great... oh no!
Congrats to @nicoleozer, who is the new executive director of the EFF.
As age verification laws begin to roll out across the globe, some of us simply have to exist for our phones to know how old we are. (via @hern)
Meanwhile, clearly this is the biggest cyberattack of the year so far, if true.
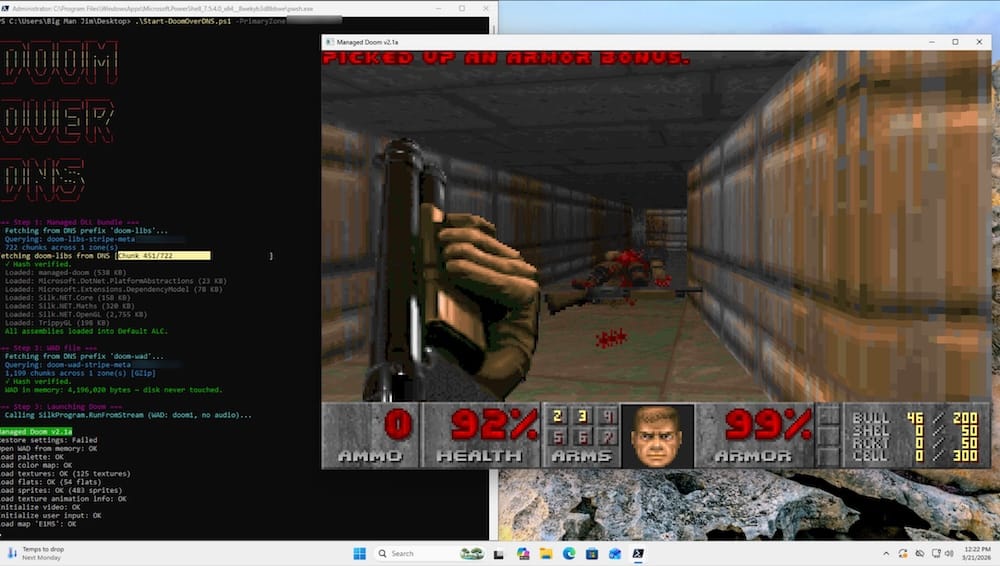
They say whenever there's an outage, it's almost always DNS, except in this case when it's…DOOM?! Yes, that's right, we're back with the latest edition of What Can Doom Run On is here and I'm extremely impressed to see that someone has managed to get Doom to load over thousands of DNS TXT records. (Yes, you can use DNS to host files… and yes, even malware.) The full code is on GitHub, and there's a write-up for the nerdicurious like me. Not to be outdone: Niels Leenheer only went and made the whole game out of CSS style code, so it loads pretty much natively in any browser. Just incredible work here.
And, an interesting nugget for macOS 26.4 users: Your Mac will now warn you if you paste something into your Terminal that could harm your computer, such as instantly installing malware from the web. This is a common tactic called ClickFix attacks. (I have a whole blog about these attacks!) @malwarezoo has a good thread on X explaining how this new macOS security feature works.
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
Meet this week's cybercat is Аня (Anya), who according to her human hails from Russia and now lives in the warmer Florida sun. Here, Anya can be seen keeping a close watch on her human from her cozy hacker house. Thanks so much to akbatten for sending in!

🐈 Keep sending in your cyber cats! 🐈⬛ If you have a cat or a non-feline friend, send me an email with their photo and name, and they will be featured in a later newsletter!
~ ~
SUGGESTION BOX
And I'm outta here! I won't keep you for another moment, this was a really busy week in security.
Please do get in touch if you have anything to share. I can be reached by email if you want to drop me a line about anything in the newsletter, or for an upcoming edition. I hope you have a great rest of your weekend, and a bright and sunny week. The thought of warmer weather just around the corner here on the U.S. east coast gives me considerable delight.
See you next Sunday for your usual roundup from the world of cyber.
All my best,
@zackwhittaker