this week in security — may 10 2026 edition
THIS WEEK, TL;DR
Edtech giant Instructure hacked (again), school logins defaced with threat to publish stolen data
Harvard Crimson: Rough week for millions of students who found themselves briefly locked out of student data system Canvas, run by edtech giant Instructure, which had its third(?) hack of late alongside a major data breach affecting students, teachers, and staff around the world who use the software. The ShinyHunters hacking group said it stole names, students' private email addresses, and gobs of messages between students and staff, which can include highly sensitive communications. The hackers used their access to display an extortion message on the login screens of schools that use Canvas (here's how). The hackers aimed to cause disruption to add pressure on their extortion tactics. Instructure is now in the midst of a huge incident response, though you might not easily find the page. Cruel for the schools who left Blackbaud and PowerSchool after their hacks only to face this one... Your friendly neighborhood hacker @racheltobac has answers for students. At least the kids seem to be taking the situation pretty well.
More: Krebs on Security | TechCrunch | Associated Press | DataBreaches.net | 404 Media ($) | Bleeping Computer | @jason_koebler
CISA says CopyFail bug affecting Linux users now under active attack
The Register: U.S. cyber agency CISA says the CopyFail bug affecting a ton of different Linux distributions since 2017 is now being used in active hacks. It was a matter of time given the relative ease in which this bug can be exploited to gain root access to vulnerable systems. But the real danger is when the bug is attached to a remote exploit, such as a phishing link or a ClickFix-style attack. By gaining root, attackers can access all of the data and operations on an affected Linux server, which isn't great for shared Linux hosts that run a bunch of virtual machines! Given the risk, CISA gave the rest of the civilian federal government until May 15 to fix. Not to be outdone: A new Linux kernel bug called Dirty Frag has similar properties to CopyFail, granting an attacker to escalate their regular access to root. Some remediation advice on GitHub.
More: CISA | Cyberscoop | Microsoft | @threatintel | Gabriel Garrido
Chinese-language hackers accused of planting backdoor in Daemon Tools
Securelist: A new "supply chain" attack compromised the Windows PCs of several thousand people who use the disk imaging software Daemon Tools. Suspected Chinese-language hackers slipped a backdoor into the freeware software a month ago, allowing the hackers to focus in and hack a dozen or so specific computers with secondary malware — mostly government, retail, scientific and manufacturing in Russia, Belarus, and Thailand, for reasons not yet clear. This is the latest hack targeting software and its users, after Notepad++ and CPUID earlier this year. Honorary mention to JDownloader, whose website was hacked to deliver malware.
More: Daemon Tools | TechCrunch | Ars Technica | @campuscodi
Braintrust breached, tells customers to rotate sensitive keys
TechCrunch: AI evaluation startup Braintrust told all of its customers to rotate their API keys and other secrets after a breach of its AWS account, which stored the private keys that its customers use for accessing cloud-based AI models. It's not clear how the breach happened, but one Braintrust user said the hack could have "downstream implications for affected customers." Nobody has taken credit for the breach just yet, but many web-focused companies like Braintrust are being targeted because they hold secrets, like API keys, which allow access to their customers' data. For its part, Braintrust counts a few well-known companies as customers.
More: Braintrust | SecurityWeek | @jaimeblascob | @elgringomexicano
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for access to exclusive articles, analysis, and more.
Or, you can submit a one-time tip to show your support!
~ ~
THE STUFF YOU MIGHT'VE MISSED
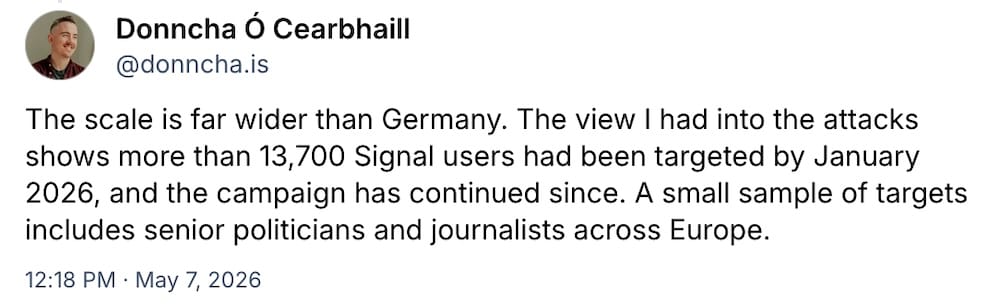
Amnesty researcher turns Signal-linking hack on its head
Donncha Ó Cearbhaill: If you get a random "Signal Support" message, it's probably an attempt to compromise your Signal account. Amnesty Lab tech head @donncha explains how the scheme works — thought to be very similar to how Russians use phishing lures to target Ukrainians, but actively part of a campaign targeting senior German and EU politicians and beyond, per Der Spiegel ($). Use the Signal registration lock feature!
Alberta voter list leaks 3 million names online
CBC: A provincial list of voters for Alberta containing 3 million names was posted online by a Canadian separatist group. The list was ordered to be taken offline, but the circumstances around the case seem very odd, and authorities are investigating the leak from an "official voter list." Interestingly, the database is salted with a handful of fake names to help trace a leak in the event of a breach. Smart!
Vibe coded apps are exposing corporate and personal data online
Wired ($): Thousands of AI-developed (aka "vibe-coded") apps developed on platforms like Lovable, Base44, Replit, and Netlify, which let people build apps in seconds, are a hot mess of security flaws. Many of the apps that are made expose users' private data. The companies put much of the blame on the developers themselves… which… uhh…
This deepfake tech used by scammers is powerfully accurate
404 Media ($): A newly discovered powerful "deepfake" software typically used by scammers, and obtained by 404 Media, is alarmingly good at spoofing people's appearances in real-time, per reporting by @josephcox. The software, dubbed Haotian AI, has no glitches and no delays, presenting a whole new challenge in detecting video forgeries. Cox has reported on the cybercriminal world for years, so for this to take him by surprise suggests that this tool is as advanced as it seems.
Ivanti, Palo Alto warn of zero-days under attack
Bleeping Computer: A new Ivanti zero-day just dropped, for all those who celebrate or keep count. The bug in its EPMM mobile endpoint manager allows remote code execution on an affected server (CVE-2026-6973), and Ivanti has confirmed exploitation, because hackers love cracking into MDM tools as a way to target people's devices. Also: Palo Alto Networks says attackers have exploited several of its firewall models (CVE-2026-0300), with watchers blaming the attacks on China.
This internet-connected bladed robot mower has flaws that make it easily hackable
The Verge ($): Great work here disclosing multiple information leaks and remote access flaws in a popular bladed robot lawn mower by Yarbo, which said it would fix the issues. The full research is worth the read, and the litany of bugs are eyewatering (including the precise location of where a robot is located without needing credentials!). "Honey, I'm just getting run over by a robot lawnmower for journalism!" — @seanhollister, probably.

~ ~
OTHER NEWSY NUGGETS
States sharing data with ad giants: Google, LinkedIn, Meta, and Snap sent personal and health information of residents who signed up for health insurance through their U.S. state's exchange. This is due to the use of hidden website pixels that collect user data and share it with advertisers under the guise of providing website analytics. Some states have since pulled the trackers following a Bloomberg ($) investigation. (via @dmehro)
Stealthy screensaver cyberattack: A customer support staffer at SSL/TLS certificate provider DigiCert was hacked and fraudulently obtained some customer certificates. The hackers used a screensaver file disguised as a screenshot to hack the support staffer. This is because screensavers can run code, and have been abused to plant malware before. DigiCert said in a post-mortem that it revoked 60 certificates, many of which were used to sign the Zhong Stealer malware. (via HelpNetSecurity, Bugzilla)
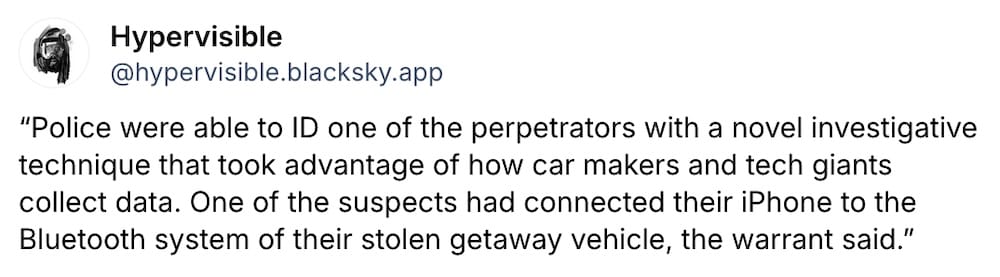
Hey Siri, play getaway music: Forbes explains how police chain data requests together to get the information they want. In the case of an armed robbery, one of the accused allegedly connected his iPhone to his getaway car, which left behind a random Bluetooth identifier. When this identifier was used to subpoena Apple, the cops found the owner of the suspect's phone because it was connected to his iCloud account. (via Forbes ($), @thomasbrewster)
Arctic Wolf, Cloudflare slash jobs: Security giants Arctic Wolf cut around 10% of staff (~250 jobs), citing its move to save money so its sausage-fest executive suite can invest more in AI. Cloudflare, meanwhile, cut some 20% of its workforce (~1,100 jobs), also citing its move to do more with AI. Layoffs are caused by a failure of a company's leadership. (via Reuters ($), The Register)
Telcos exploited to track people: With the help of Citizen Lab's recent research, Haaretz digs into how flaws in telcos and cellular providers are abused to gain access to the global cell network, allowing surveillance vendors and government spies to tap people's real-time location data and more. (via Metacurity ($), Haaretz)
~ ~
THE HAPPY CORNER
Stop! And breatheeeeee. This is the happy corner.
I can't not start by saying a huge congratulations to friend-of-the-newsletter @yaelwrites for casually winning a Pulitzer Prize(!) this week for her incredible work with @dakekang, @byrontau, Aniruddha Ghosal, and Garance Burke, covering how Silicon Valley enabled mass detention and surveillance across China. The series also included how U.S. authorities run secret surveillance programs around the United States.
Also: A huge congratulations to @raphae.li and @ajvicens for their Pulitzer Prize-winning work at Reuters, exploring the retribution faced by many in the wake of the killing of Charlie Kirk. Just absolutely amazing to see this award go to two amazingly talented cyber reporters.
Plus, a shoutout to the now-two time Pulitzer Prize winner @seamushughes, who does amazing work at Court Watch; and the excellent @drewharwell whose work was picked as a Pulitzer finalist for his work covering ICE and Trump's immigration crackdown.
These are all amazing reporters — some of whom I'm really fortunate to know as friends — and whose work deserves your attention.
In some news from… me? (Rare!) On Monday, I sued the Justice Department and the FBI for records under the Freedom of Information Act. I wrote some words explaining why I can now take on Whittaker v. Justice Department, and with my deepest gratitude and thanks for the support from the excellent people at the Reporters Committee for Freedom of the Press for representing me in this matter.

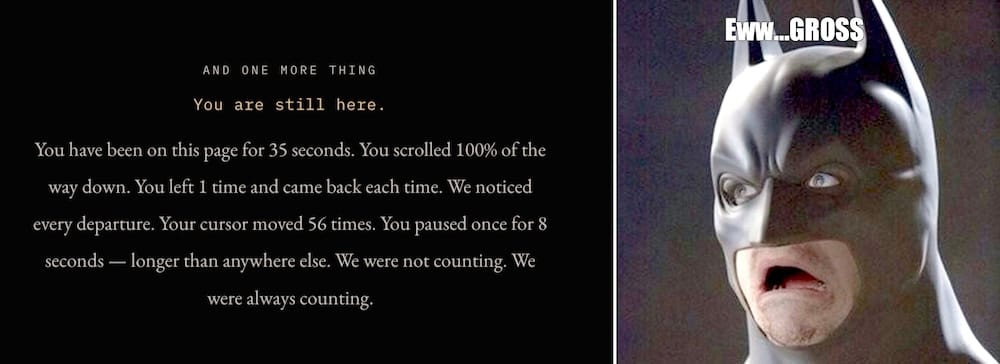
Meanwhile: This website tells you what it knows about you and it's eerily creepy. I use an ad-blocker (and I recommend that everyone does!) but even the less-invasive bits of data that this website can see about me gave me the chills. Case in point:
Bonus thread on my Mastodon profile asking for people to share things that they were proud of this week, and hooooboy I got real misty-eyed at some of these. You are all amazing.
And finally, this week… pssssts loudly… Hey kids, you wanna break into a building? Turns out you can — and legally! This Reddit AMA with TrustedSec's Paul Koblitz is a really interesting look at physical penetration testing, aka testing the security of real-world buildings and things to help identify physical security flaws and weaknesses.
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
This week's cyber cat is Maddy, whose human tells me that she moonlights as an information warfare specialist for Britain's MI6. Not a surprise, us Brits do love to have cats serve in government. A big thanks to Alex S. for sending in!

🐈 Send in your cyber cats! 🐈⬛ Got a cat or a non-feline friend? Send me an email with their photo and name and they will be featured in a later newsletter!
~ ~
SUGGESTION BOX
Alright, let's wrap this one up for another week. Thank you so much for joining me for another edition of this week in security. I can't tell you enough how much it means to me that you read and support this newsletter. Can you believe we're almost at eight-years of weekly dispatches? 👀
Please do reach out if you have anything you want to send in for the newsletter next week, or anything else that's coming up that you think would be cool to include. I love to hear from you — and your cybercats — (tell them "psssp pssp psssp," they'll get it).
I hope you have a great rest of your day and your weekend, and I'll catch you next Sunday with everything from cyber-land that you need to know.
See ya',
@zackwhittaker
