this week in security — may 3 2026 edition
THIS WEEK, TL;DR
Hackers are exploiting a login bypass flaw in cPanel and WHM, used to manage millions of web servers
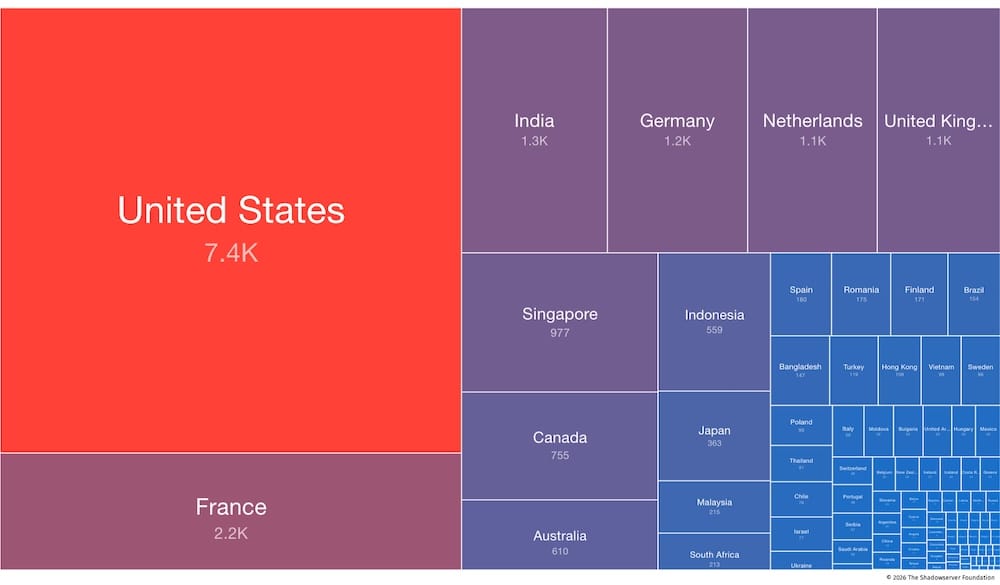
The Register ($): Bad news for potentially millions of domain owners whose web servers are run by cPanel and WebHost Manager (WHM), two widely popular server admin panels used by web hosts to control and manage their websites, emails, databases, and more. The bug, tracked as CVE-2026-41940, affects all supported cPanel/WHM versions, including 11.40 upwards, so that's… practically everyone affected. Major web hosts like Namecheap, Hostgator, KnownHost, and others patched their customers' systems already, since there was already evidence of attempted exploitation. Another cPanel product, WP Squared, which manages WordPress installs, was also patched. CISA says hackers are using the flaw in active hacking campaigns, and now it's been seen in mass-ransomware attacks. If your server runs an affected cPanel/WHM version, update today!
More: HelpNetSecurity | Bleeping Computer | Canadian Center for Cyber Security | Censys | TechCrunch ($) | GovInfoSecurity | watchTowr Labs | Shadowserver Foundation
CopyFail bug threatens a ton of Linux distros since 2017
Ars Technica: It's been some time since we've seen a major bug affect Linux, but a major bug dropped this week affecting consumer PCs all the way up to servers in data centers. CopyFail is a privilege escalation bug that allows regular Linux users to become admins. Worse, the bug is being exploited with as little as a single line of code. The bug was introduced in 2017 and affects pretty much every major Linux distribution going. The Linux kernel team patched the bug, but many Linux distributions haven't rolled out patches yet, setting off a scramble to fix before malicious attackers can hack their users. There's now a rush to patch systems before exploitation becomes more widespread.
More: CopyFail | The Verge ($) | Joshua Drake (LinkedIn) | @wdormann | @taggart-tech
U.S. Supreme Court seems mixed on legality of geofence warrants
SCOTUSblog: The U.S. top court heard oral arguments questioning the legality of "geofence" search warrants, which allow cops and feds to mass-search the location history databases of tech giants (like Google) to determine who was at a specific place at a particular point in time. Critics say this is the reverse of how the Fourth Amendment is supposed to work, where cops have to show evidence of a crime linked to a person first. The top court seemed mixed on whether these warrants flat-out violate the constitution, but opened the door to possibly narrowing how broad (and for how long) these warrants can be, if not least to minimize ensnaring entirely innocent people whose data also gets scooped up by these warrants. NPR has a good video explainer on the issue, by the way.
More: CNN ($) | Politico ($) | Lawdork | TechCrunch ($) | @chrisgeidner | @orinkerr
Checkmarx confirms data stolen in recent supply chain attack
Ars Technica: The excellent @dangoodin explores the recent spate of security incidents to beset cybersecurity company Checkmarx, which found itself both a target as well as a delivery mechanism for malware. The company's woes began with a breach of Trivy, an open-source vulnerability scanner, which allowed access to its customers, including Checkmarx. Now, Checkmarx now says it's had a data breach linked to the incident. Bitwarden was also hit (I mentioned this last week) by the same Trivy breach. The interconnected natured dependencies of tech companies these days means security incidents are seldom limited to just one company. Not to be outdone: Trellix (formerly FireEye) says some of its code repos were compromised in a recent hack.
More: SecurityWeek | The Register | SC Media | SecurityBoulevard
Data Breach Palooza: Carnival, Itron, Medtronic, Pitney Bowes, Vimeo
Alright, we have another important roundup of data breaches to blast through in a flash… *start the clock*... American utility meter provider Itron says it was hacked but customer meters appear unaffected (so far)... Medical device maker Medtronic confirmed a breach and extortion attack said to affect over 9 million records of customers' personal data, which DataBreachToday says is at least the fourth hacked medtech firm in recent weeks… *breathes in*... Mailing giant Pitney Bowes had 8.2 million customer records stolen, including postal addresses, per The Register… video sharing site Vimeo was hacked… cruiseliner giant Carnival is probing a breach involving 8.7 million customer records… and… ADT was sued for a theft of 5.5 million people's records. *stops clock*.
More: Bleeping Computer | DataBreaches.net | Bloomberg Law ($)
~ ~
~this week in security~ is my weekly cybersecurity newsletter supported by readers like you. Please consider signing up for a paying subscription starting at $10/month for exclusive articles, analysis, and more.
Or, you can submit a one-time tip to show your support!
~ ~
THE STUFF YOU MIGHT'VE MISSED
U.S. firms embrace Sam Altman's eyeball scanner, even as the world pushes back
Rest of World: Sam Altman's creepy eye-scanning company has faced investigations and been halted by governments, yet has still recently partnered with Docusign, Tinder, and Zoom to verify their users, according to Rest of World. Altman's aim is (allegedly) to cut down on deepfakes, in part from generative AI, which is… Altman's main venture. (This all feels very "firefighters starting fires" to me.) Also: @ridogi notes that therapy provider Headway will soon require identity verification using third-party service Persona, which Discord previously used but later dropped. This might deter a good number of people from using the service to seek therapy.
How AI is helping to supercharge attacks by script kiddies
The Verge ($): Cyber freelancer and friend of the newsletter @yaelwrites explores how "script kiddies," i.e. hackers without many technical skills, are able to use AI to enhance their capabilities, which was previously not possible just by running simple scripts of code. This is an interesting deep-dive, citing in-the-know experts, looking at today's state of how security defenders are planning for an incoming "patchpocalypse."

Former NSA boss during Snowden leaks reflects on the agency's cybersecurity
Dark Reading: In a recent podcast, Chris Inglis, who was one of the senior executives at the National Security Agency during the Edward Snowden leaks in 2013, walks readers "through the mistakes that NSA made" at the time. This includes what the NSA should have done in hindsight to prevent the massive breach of classified files. There are learnings in here that can no doubt help in other organizations today.
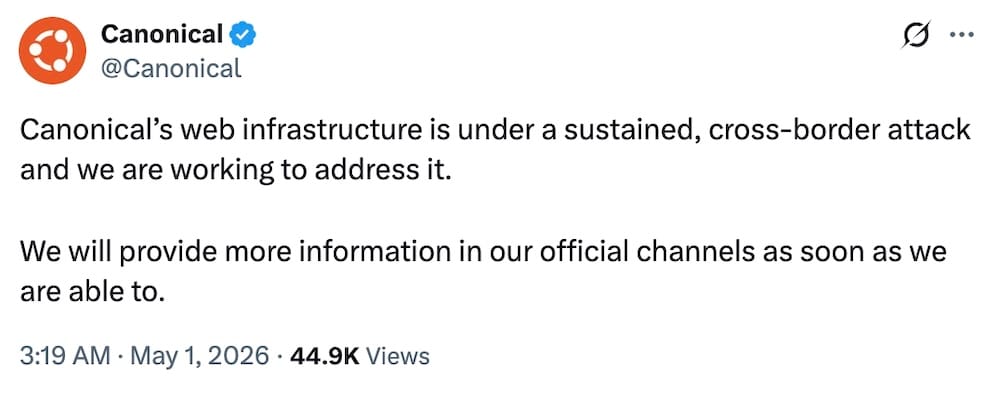
Ubuntu Linux services hit by outage linked to DDoS attack
Ars Technica: Online services for Ubuntu Linux have been knocked offline for more than a day (and ongoing), preventing users from updating packages and installing new ones. The website of Canonical, which maintains Ubuntu, was also up and down. The company says it's experiencing a "sustained, cross-border attack," with a hacktivist group claiming to use a DDoS-for-hire site called Beamed. A Reddit thread has all the latest updates.
GitHub rushed to patch bug that allowed access to private code repos
The Verge ($): Cloud giant Wiz found a "remarkably easy to exploit" bug (👀) in GitHub's internal infrastructure that could've allowed attackers to access millions of public and private code repositories. GitHub said there was no evidence of past exploitation, but it's hardly likely to assuage fears from long-suffering users who've had to leave GitHub over the platform's growing instability under Microsoft's ownership.
China pressured Zambia to cancel RightsCon digital rights conference
Wired ($): RightsCon, the world's largest digital rights conference run by AccessNow, was set to be held in Zambia this week… until the government in Lusaka pulled the plug. AccessNow squarely blamed Beijing for putting pressure on Zambia "because Taiwanese civil society participants were planning to join us in person." Wired ($) has more, as does 404 Media ($) for subscribers.
~ ~
OTHER NEWSY NUGGETS
NSA has Mythos, but CISA doesn't: Staffers at the U.S. cybersecurity defense agency CISA are without access to Anthropic's unreleased cybersecurity AI model Mythos, whereas the NSA does, for some reason. CISA says the lack of access is impeding its ability to protect the federal government domain. NSA (which does offensive hacking) has been granted access, despite its parent department, the Pentagon, labeling Anthropic a "supply-chain risk" in retaliation for not allowing generals to use its AI for domestic mass surveillance and killer robots. (via Forbes ($), Axios ($))
Canada nabs SMS blaster: Toronto police have levied dozens of charges against three men for allegedly using SMS blaster equipment to send spammy text messages to "thousands of devices at once" across the city. The police also say these devices also mess with the cell networks by preventing people from calling the emergency services. Below is an example of an SMS blaster seized in the U.K., given that Canadian officials said they're not releasing photos of this particular blaster just yet. (via Toronto Police)

Sri Lanka loses $3 million in email scams: Rough week(s) for Sri Lanka after losing at least $3 million in separate business email compromise attacks, whereby hackers break into emails or financial systems, change bank details to that of the attacker, and divert funds intended for payment. Australia said it's missing a payment, suggesting the Sri Lanka breaches are worse than believed. (via BBC News ($), TechCrunch ($))
ChipSoft hackers 'destroyed data': Netherlands patient software provider ChipSoft says hackers deleted the data that they stole and the data won't be published anywhere, according to a statement. The company wouldn't say if it paid the hackers a ransom demand (it probably did). Here's a live shot to the hackers "deleting" the data:

Chinese government hacker in U.S. custody: The DOJ successfully extradited a suspected Chinese government hacker to the U.S. to face trial. Xu Zewei is accused of working for the Hafnium hacking group, which stole COVID-19 research but is also best known for mass-hacking Exchange servers back in 2021. Of course, it's somewhat obvious that government hackers might be arrested if they travel abroad, per Reuters ($), but also presumably this goes both ways as well for Western hackers... (via Justice Department)
FISA? WTF? JFC! Let's check in on American lawmakers' efforts to reauthorize or modify U.S. surveillance la…aaaand they pushed it back by another 45 days. The short-term extension will last until around June 14-ish. (via Axios ($), The Hill)
~ ~
THE HAPPY CORNER
At last! Enough with that nonsense. Let's enjoy the gentle warmth of calm and wonder in the happy corner.
I don't have any better out-of-office replies from last week, alas, but I do really want this mechanical auto-email greeter.
In much-needed good news: Canada has decided to ban crypto ATMs, and not a moment too soon. There are around 4,000 crypto ATMs across Canada (soon to be none!) that are a hotbed of fraud and scams. This is definitely a good move. (via @parismarx)
Moving on. When hump-day doesn't go your way:
Bug bounty boss and newfound bird landlord @cje found house finches in his sunroom office and set up a live-streaming birdcams, with a little sprinkling of AI to auto-write a short journal entry each day. It's low-stakes but fun, and I love to see this. (I have a personal interest in this after pigeons nested on my balcony.)
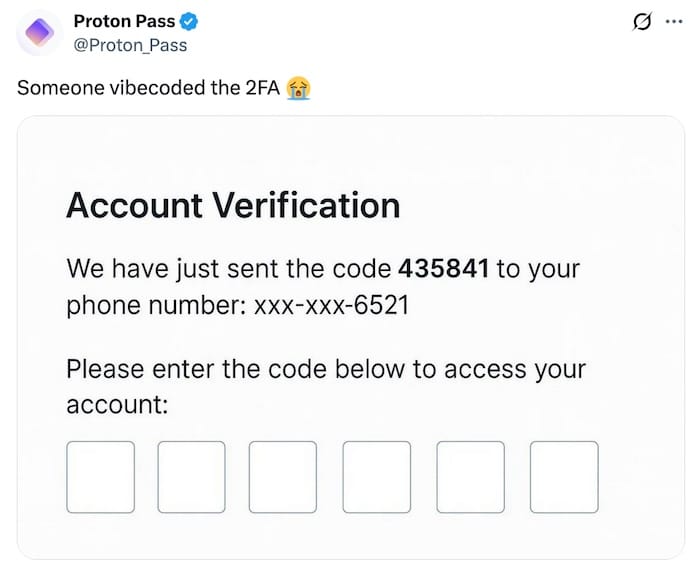
Meanwhile: This is the modern-day equivalent of "admin/pass".
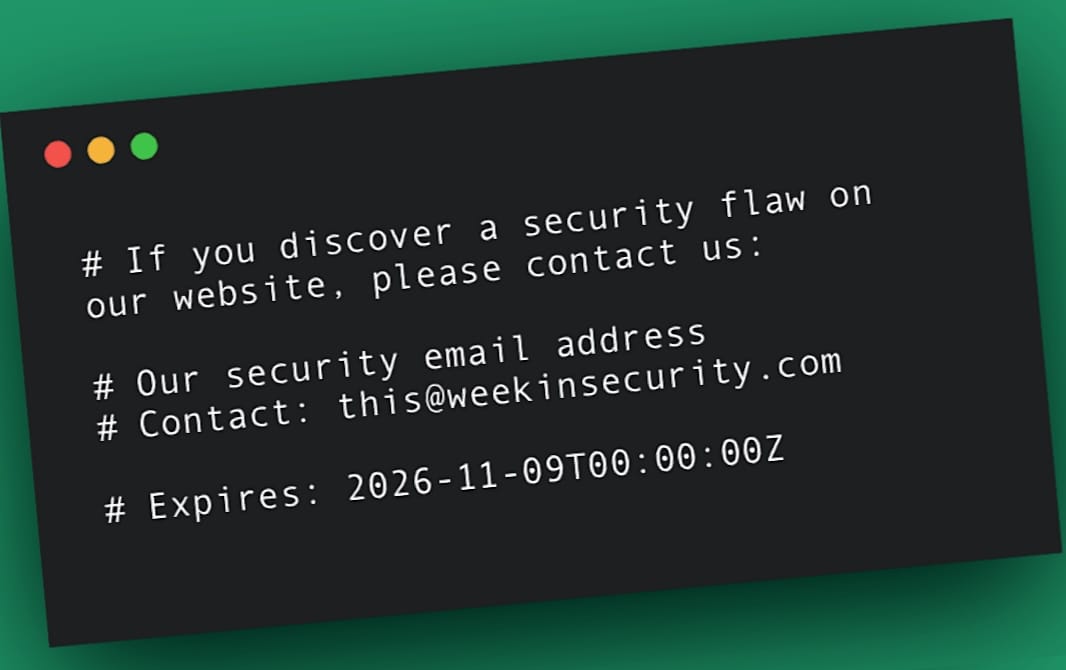
And lastly this week. Come for the short anecdote about how I gave one corporate executive the ick, and stay for a bunch of reasons why every company and organization should make it easy for anyone(!) to alert them to security flaws and data leaks. Here are some words from me, a freebie read from me to you. Please share if you like it!
Got good news to share? Get in touch! this@weekinsecurity.com.
~ ~
CYBER CATS & FRIENDS
This week's rare trio of cyber cats features Bruce (the black and white kitty), Tonic (the tabby cat), and Gin (the void floof), who can be seen here in a bundle of trouble after a busy morning hacking into their local pet store's computer systems. That's the face of a proud hacker cat who just had 13 tons of treats shipped to the house. Triple thanks to Tori S. for sending in!

🐈 Keep sending in yer' cyber cats! 🐈⬛ If you have a cat (or a non-feline friend), please send me an email with their photo and name, and they will be featured in an upcoming newsletter!
~ ~
SUGGESTION BOX
That's all for this week! Thank you so much for reading and subscribing to my newsletter. It really means the world. I hope you enjoyed this busy edition. If you're hankering for more, feel free to check out my articles (and reach out if there's anything specifically you would like me to cover!)
If you have anything to share for next week's newsletter (or anything else coming up), please do get in touch. It makes my day hearing from you — especially if there's a cybercat attached!
I'll be back next week as usual. Until then, have a great rest of your week.
Until next, my friends.
@zackwhittaker
